Management
Management
Management
Trusted by 13,500+ organizations


it’s a journey
How can you ensure that your organization is more secure tomorrow than it is today?
Features
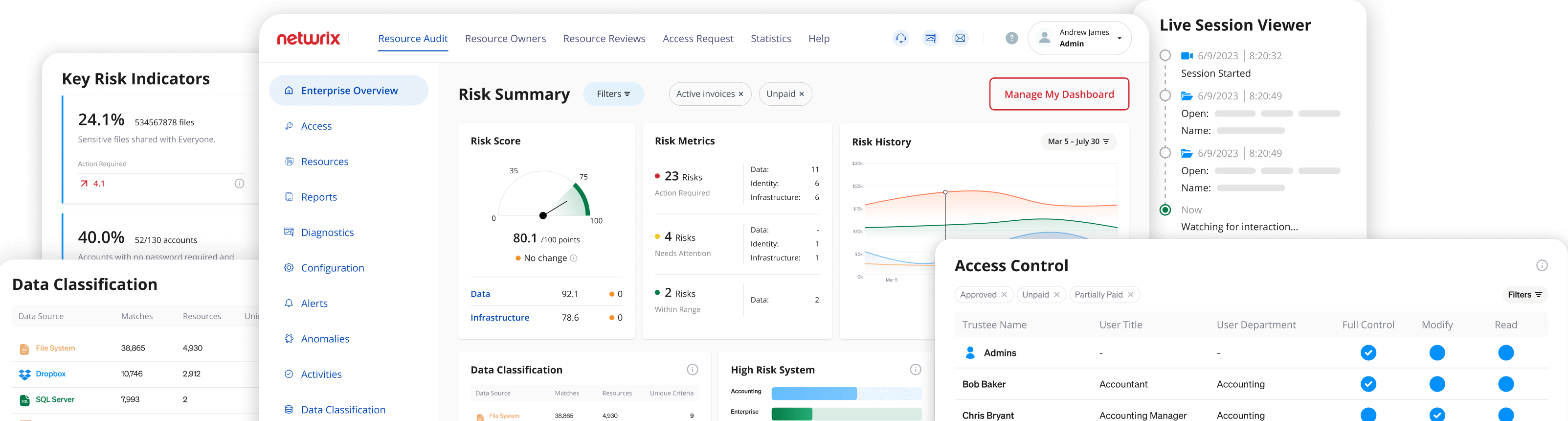
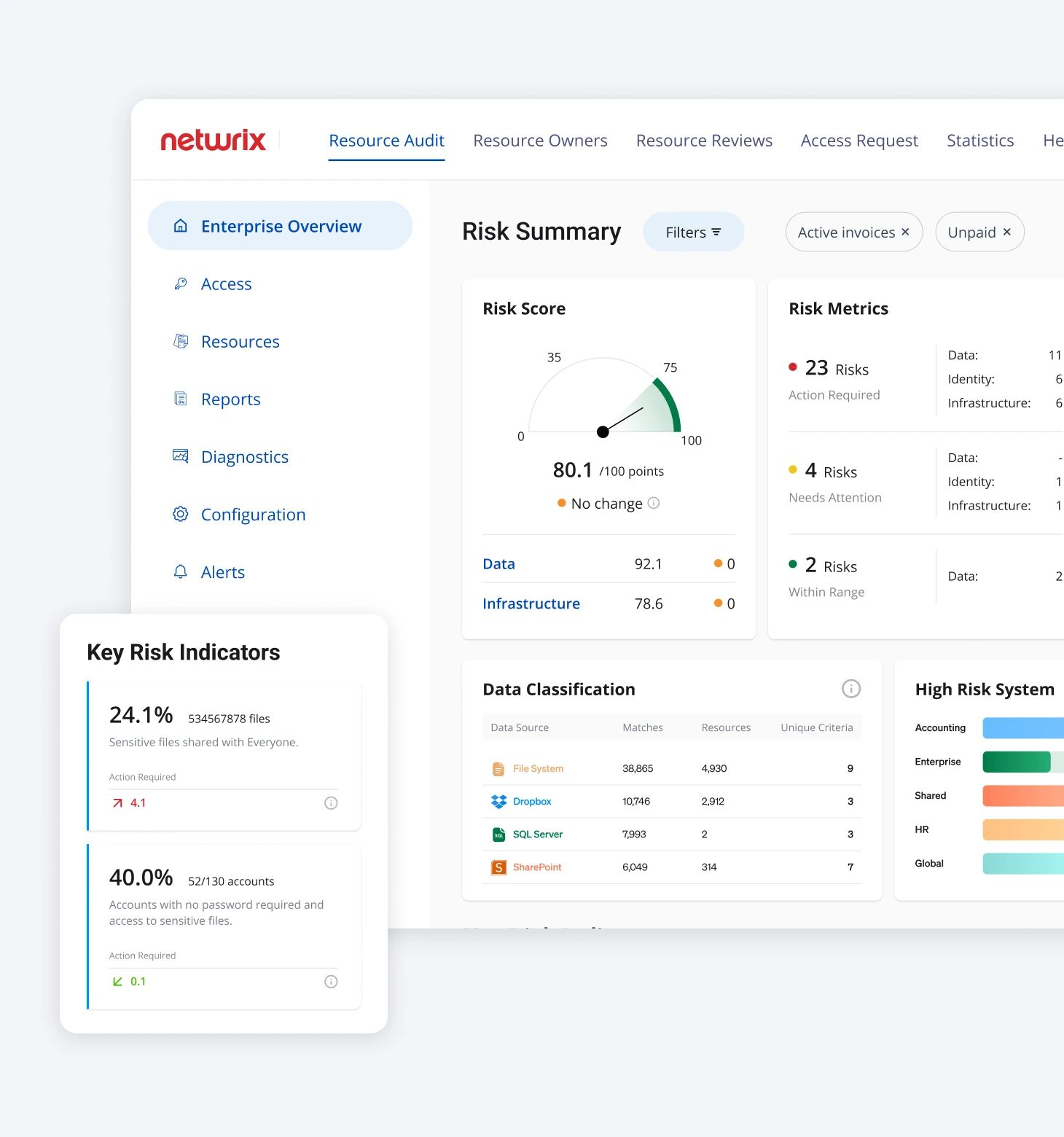
Risk Assessment
Discover and mitigate a wide variety of data and identity risks due to misconfigurations, vulnerabilities, and violations of policies, best practices, or desired states.
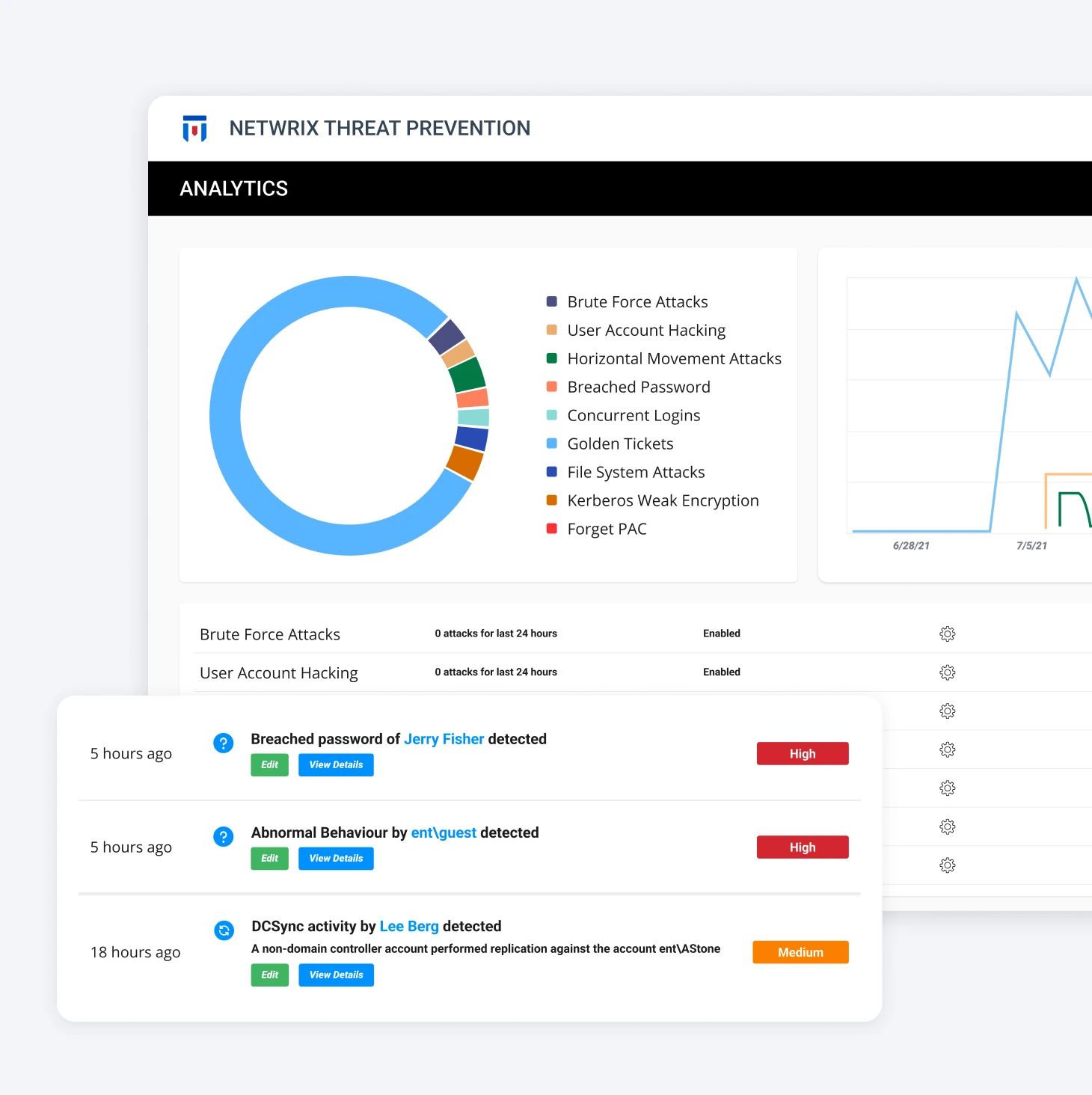
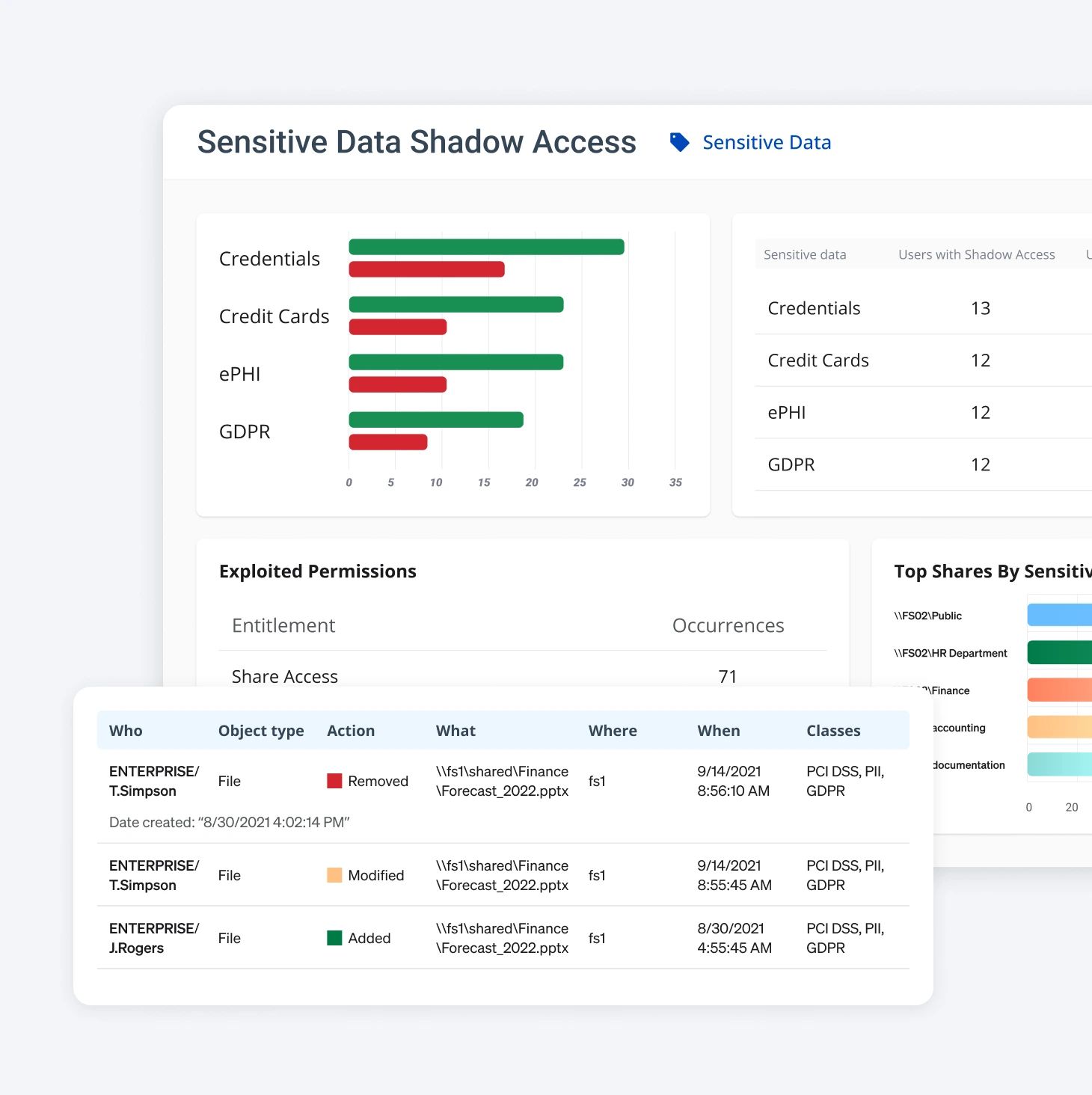
Threat Detection & Response
Monitor your IT environment for threats in real-time based on known frameworks, machine learning, and behavioral analytics. Flag real threats while reducing false positives.
Auto-remediate confirmed threats. Get a detailed report containing attack timelines, actions taken, vulnerabilities exploited, and more.
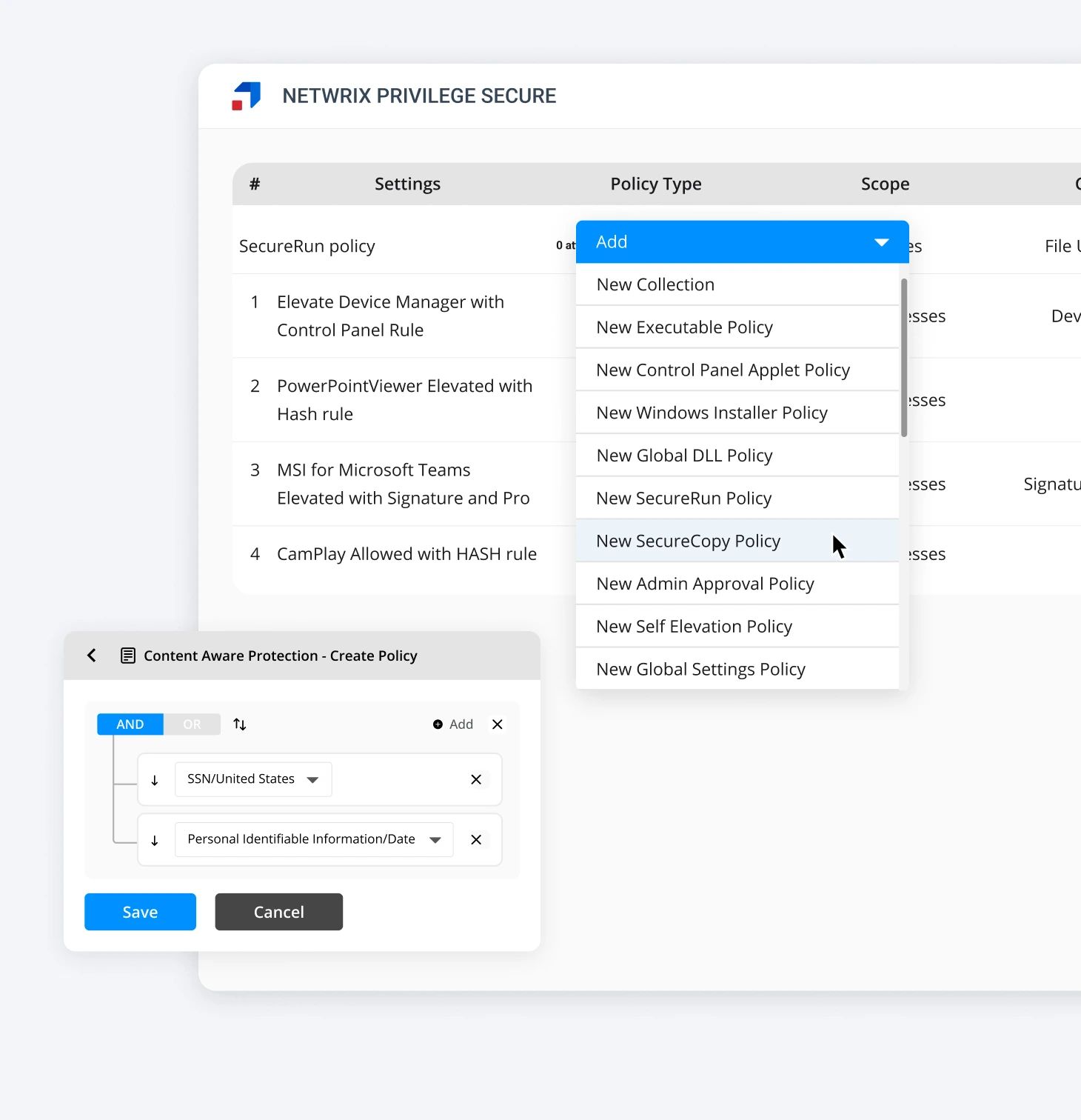
Policy Enforcement
Create & enforce security policies across ADs, endpoints, identity, network, etc. Manage user permissions, app settings, password rules, etc.
Automatically block risky behavior & remediate policy violations. Secure your environment without disrupting daily operations.
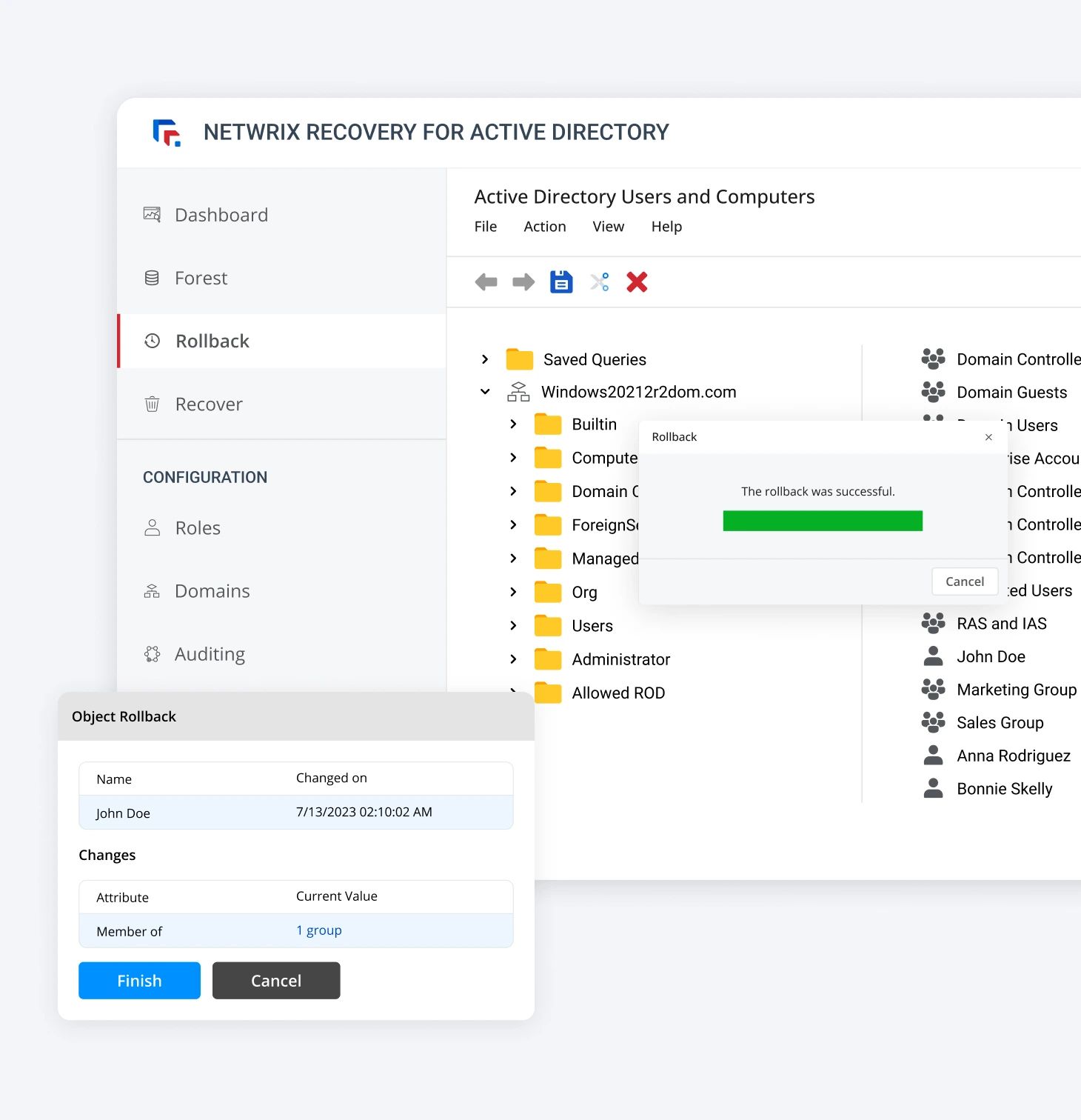
Rollback & Recovery
Manage access, policies, and identities to ensure the right users have access to the right resources at the right time. Reduce IT workload with automated workflows and self-service.
Management
Instantly roll back individual changes or restore your system to a previous state. Fix misconfigured permissions, group policies, and application settings.
View a full timeline of changes for quick troubleshooting. Automate backup creation to ensure reliable recovery points.
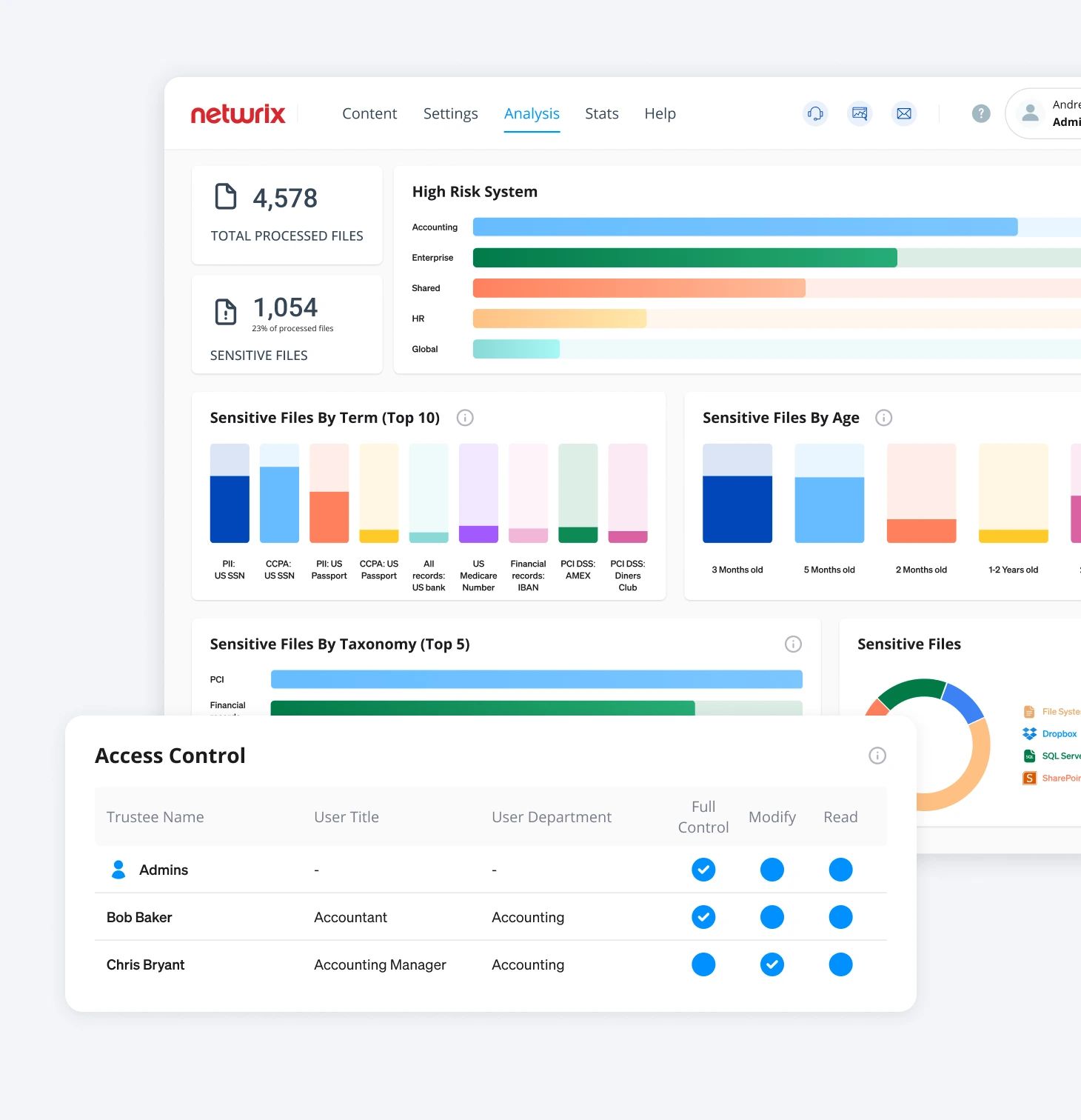
Governance & Compliance
Streamline compliance with automated monitoring and audit reporting.
Log access rights & data protection actions in real-time. Generate comprehensive audit reports in a few clicks. Prove compliance with industry regulations, including HIPAA, GDPR, ISO, NIST, etc.
Integrations
Integrate with Microsoft Office 365, NetApp, Oracle, VMWare, SharePoint, and other enterprise platforms.
Connect with SIEM, ITSM, and identity management tools for automated workflows. Or build custom integrations with our API.

Get the comprehensive protection
you need
Today’s IT ecosystems are complex, but every element of the environment still needs to be secured and continuously monitored. That includes all the different types of data you store and process, the applications you use, and all your workstations, servers and network devices. Netwrix provides an integrated solution set that covers it all.
See why over 13,000 organizations
worldwide
rely on Netwrix
Horizon Leisure Centres ensures GDPR compliance while saving £80,000 annually.
Vodafone complies with PCI DSS and protects customer PII, saving countless hours annually.
Eastern Carver County Schools maintains least privilege principle to secure data of 9,300 students.
